InnoSecBW
Innovation with Cybersecurity for SMEs in Baden-Württemberg

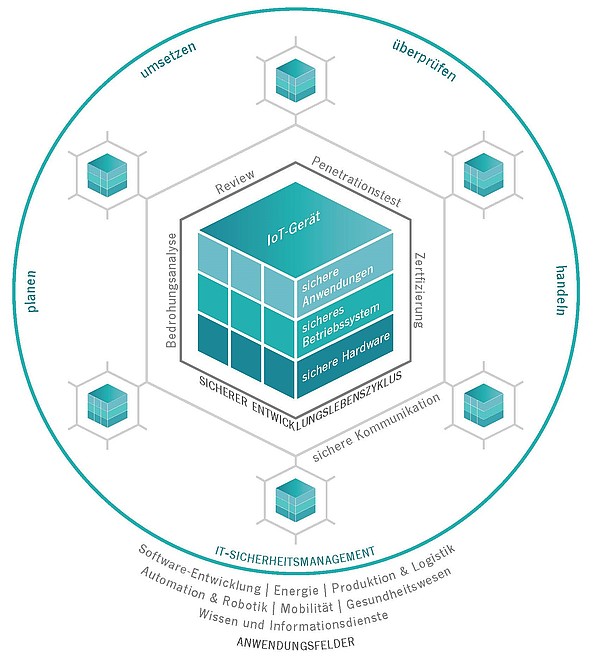
With the Competence Center for IT Security (KIS), the FZI has created a central point of contact for applied IT security research with the support of the state of Baden-Württemberg. The center offers problem-solving expertise in questions of IT security for small and medium-sized enterprises in Baden-Württemberg. At the Competence Center for IT Security, research is conducted on security technologies that are easy to understand and apply.

Ever-advancing digitalization across all industries is making it necessary for IT systems to be increasingly networked. Systems that previously operated in complete isolation are now being connected to the Internet. This leads to a greatly increased attack surface and can enable worldwide attackers to gain access. Particularly worth protecting in this context are critical infrastructures such as power plants or hospitals – attacks on such systems can have serious consequences for the safety of people and the environment.
Likewise, the Internet of Things brings with it new security challenges. To meet these challenges, pure expertise in IT security methods and mechanisms is not enough. The key to success lies in supplementing this knowledge with in-depth expertise of the respective application domain.
Innovation with Cybersecurity for SMEs in Baden-Württemberg
Static hardware/software analyses in the context of scalable edge computing platforms
Hardening of embedded RISC-V software by means of code transformations
European Digital Innovation Hub applied Artificial Intelligence and Cybersecurity
Reference sensor platform for high-precision sensor validation for automated driving
Safe use of automated shuttle vehicles in urban traffic through supporting infrastructure networking
Artificial Intelligence for Work and Learning in the Karlsruhe Region
Security across all system layers through trust chains and isolation
Competence Cluster Anonymization for Interconnected Mobility Systems
Actively addressing the challenges posed by climate change and using them as an opportunity for the German economy.